Category: Customizing Your Desktop to Improve Workflow
-

Keep capacity, keep speed: how to reduce iPhone battery stress without losing convenience in your daily routine
Read More: Keep capacity, keep speed: how to reduce iPhone battery stress without losing convenience in your daily routineYou don’t need a complicated ritual to keep an iPhone quick today and healthy next year. What matters most is when and where you move power, how warm the phone gets while doing it, and how long it lives at the extremes. A simple plan can protect capacity without slowing you down: finish charging near…
-

A long, careful plan for iPhone charging: night windows, daytime top-ups, and cool hardware habits that preserve battery health
Read More: A long, careful plan for iPhone charging: night windows, daytime top-ups, and cool hardware habits that preserve battery healthIf you want speed today and capacity next year, treat charging like a routine instead of a reaction. The goal is to move power when the phone is cool, avoid sitting at 100% or crawling to 0%, and choose moments that fit the way you live. That means anchoring a predictable night window so the…
-

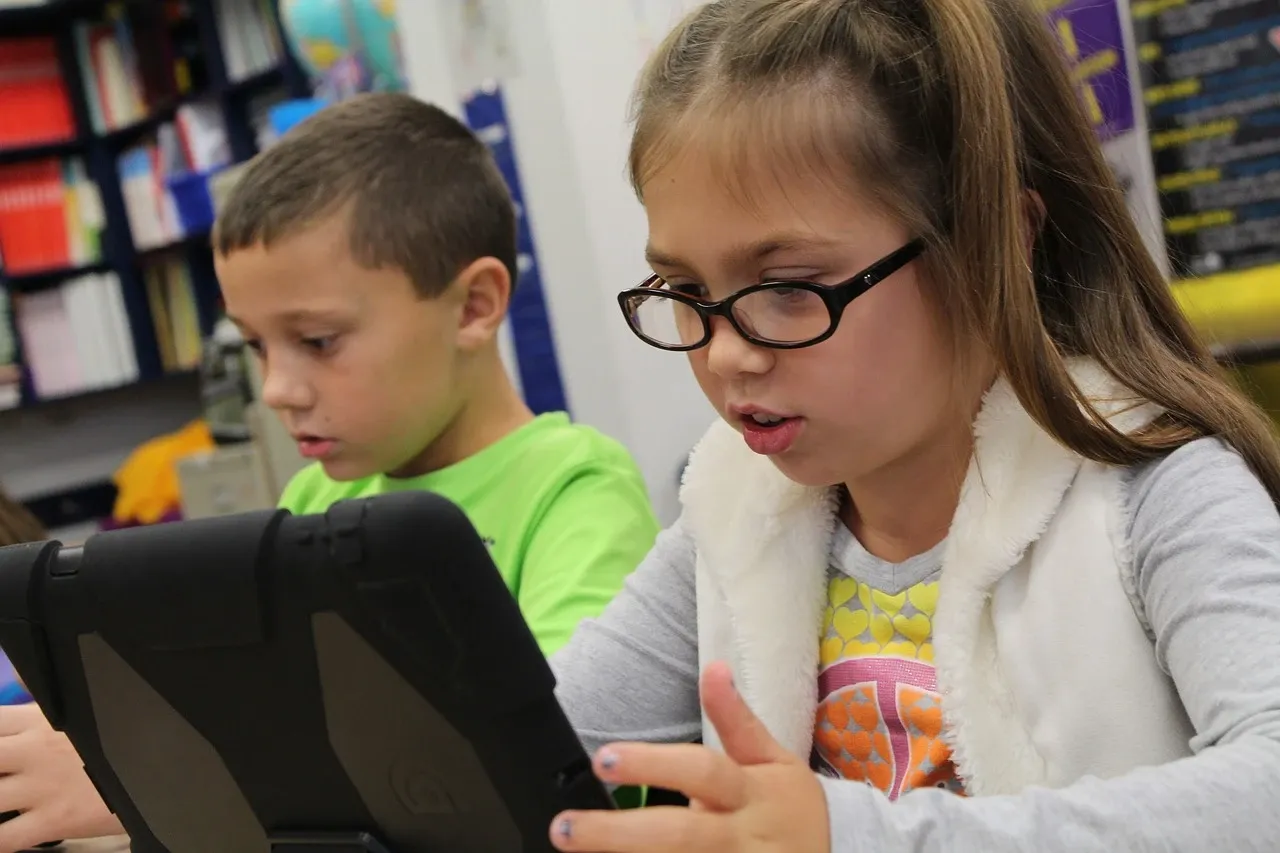
Benefits of Using a VPN for Online Security
Read More: Benefits of Using a VPN for Online SecurityUsing a VPN (Virtual Private Network) for online security offers numerous benefits, helping to safeguard your sensitive information, protect your privacy, and enhance your overall online experience. Here are some key benefits of using a VPN for online security:
-
Tips for Personalizing Your Desktop to Improve Workflow
Read More: Tips for Personalizing Your Desktop to Improve WorkflowPersonalizing your desktop environment is a great way to create a workspace that enhances your productivity and workflow. By customizing various aspects of your desktop, you can optimize it to better suit your preferences and streamline your work processes. Here are some tips for personalizing your desktop to improve your workflow:
Search
Popular Posts
-
Realtime Threat Intelligence Feeds: The Critical Foundation for Modern Cybersecurity Defense
In today’s rapidly evolving cybersecurity landscape, organizations face an unprecedented volume of sophisticated threats that emerge and evolve at lightning speed. Traditional security measures that rely on static defense mechanisms are no longer sufficient to protect against modern cyber adversaries. This reality has made realtime threat intelligence feeds an indispensable component of contemporary cybersecurity strategies,…
-
Zero-Trust Infrastructure Verification Tools: Essential Security Solutions for Modern Enterprises
The cybersecurity paradigm has fundamentally shifted from traditional perimeter-based security models to a more sophisticated approach known as zero-trust architecture. This revolutionary framework operates on the principle of “never trust, always verify,” fundamentally changing how organizations approach network security and access control. Zero-trust infrastructure verification tools have emerged as critical components in implementing and maintaining…
-
Realtime Infrastructure Failure Prediction Tools: Revolutionizing Modern IT Operations
In today’s hyperconnected digital landscape, infrastructure failures can spell disaster for organizations across all industries. The emergence of realtime infrastructure failure prediction tools has revolutionized how IT teams approach system reliability, transforming reactive maintenance into proactive prevention strategies that safeguard business operations.